RPKI Explained – Resource Public Key Infrastructure
RPKI adds cryptographic trust to BGP, preventing hijacks and leaks. Learn how ROAs, validators, and routers keep routing secure.
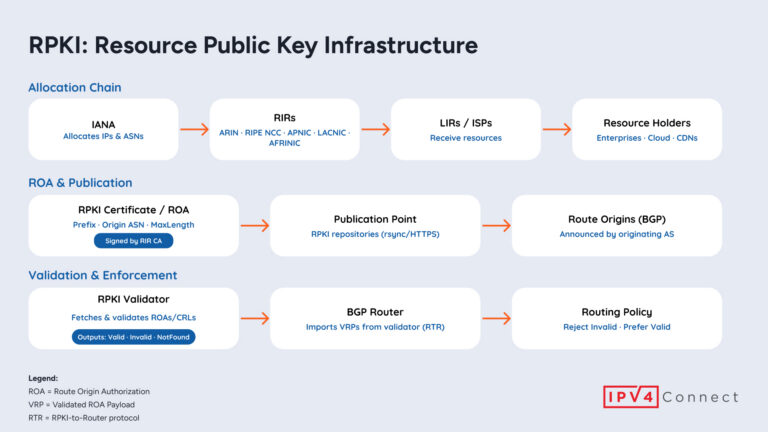
RPKI adds cryptographic trust to BGP, preventing hijacks and leaks. Learn how ROAs, validators, and routers keep routing secure.

Telecom companies face rising cyber threats and espionage, requiring cybersecurity strategies to protect infrastructure, data, and reputation

The Barracuda Reputation Block List (BRBL) flags problematic IPs for spam. Maintain secure practices and to avoid and delist.

The hidden dangers of IP transfer abuse. How cybercriminals use IP addresses for malicious activities like spam, phishing, and malware.

DDoS attacks overwhelm networks with traffic to cause disruption. This can be mitigated through proactive security measures.

Spamhaus DROP lists are essential tools in the fight against IP hijacking, that defend against DNS hijacking, and most malicious activity.
Email me when new IPv4 inventory matches my criteria.
Error: Block data unavailable.
You’ll now receive email alerts when new IPv4 inventory matches your preferences.
Are you absolutely sure you want to delete your account? This action cannot be undone.